NMIS 8.4G introduced general availability of the full authorisation and authentication model in NMIS using internal or external authentication methods. This ensures that NMIS remains an enterprise class network management system. Once authenticated a user is looked up in the internal authorisation system to determine their role, this role is customisable and extensible.
The implementation of the authorisation, limits groups of users by roles to specific things they can view and do with NMIS, and groups of devices/nodes on which they can do it. This is commonly referred to as role based access control.
The following table lists the NMIS configuration option and the type of authentication which it works with. These settings are made in /usr/local/nmis8/conf/Config.nmis.
| Method | Description |
|---|---|
| apache | Apache will perform authentication and provide an authenticated user to NMIS, which will have authorisation policies applied. |
| htpasswd | NMIS will use the users defined in the NMIS Users file, by default /usr/local/nmis8/conf/users.dat |
| ldap | NMIS will use the configured LDAP server to perform authentication Require Net::LDAP Config: |
| ldaps (secure) | NMIS will use the configured LDAP server to perform authentication Requires IO::Socket::SSL and Net::LDAPS auth_ldaps_server => 'host[:port]' |
ms-ldap | NMIS will use the configured Microsoft Active Directory (LDAP) server to perform authentication Require Net::LDAP Config: |
| ms-ldaps (secure) | NMIS will use the configured Microsoft Active Directory (LDAP) server to perform authentication Requires IO::Socket::SSL and Net::LDAPS Config: |
| radius | NMIS will use the configured radius server (Cisco ACS or Steel Belted Radius for example) Requires Authen::Simple::RADIUS Config: |
| tacacs | NMIS will use the configured Tacacs+ server (Cisco ACS for example) Requires Authen::TacacsPlus Config: |
In the NMIS configuration you can configure multiple methods which are used for auth failure, so if ms-ldap fails, it will fail back to htpasswd for example. This means if you set auth_method_1 to be ldap and auth_method_2 to be htpasswd, and login with the default NMIS credentials (and you have not changed the password), the authentication for LDAP will fail, and then authentication with the users.dat will succeed and the user will be logged in.
It is important to change your default passwords if you expect any level of security.
When accessing NMIS, you have a choice on how to handle authenticated users who do not have authorisations defined, you can reject them, or you can allow them default access.
This is so that you do not have to define every user in the system if the authentication system is providing a reduced list of users, to have the users become an operator or guest by default and be able to see all groups of devices, the following would apply.
'auth_default_privilege' => 'guest',
'auth_default_groups' => 'all',
To prevent default authorisation, simply define them as blank, which is the default in the NMIS8 Install configuration.
In NMIS versions 8.5.12G and newer you can configure optional account locking. This feature is not enabled by default as it could be abused for denial-of-service attacks.
If you set the configuration option auth_lockout_after to a positive number N, then the account in question will be locked after N consecutive failed login attempts. If the optional configuration item server_admin holds an email address, a notification email will be sent to the given administrator address.
Locked accounts can be re-enabled from the GUI: visit the System -> System Configuration -> Users page, and click on the option "reset login count" for the locked account.
From the command line re-enabling is also possibly: simply remove the file /usr/local/nmis8/var/nmis_system/auth_failures/<accountname>.json.
At great expense to Opmantek NMIS now includes a single sign on (SSO) feature, this requires cookies to work. To enable the feature, all that is required is to use a fully qualified domain name (FQDN) for your NMIS server, e.g. nmis1.domain.com and then in the NMIS configuration of all NMIS servers participating, configure the auth_sso_domain and auth_web_key in /usr/local/nmis8/conf/Config.nmis, the default is set to ".domain.com", e.g.
'auth_sso_domain' => '.domain.com', 'auth_web_key' => 'thisismysecretkey', |
Two periods are required in the domain name are required, so if your company is AJAX Cleaning and your domain name is ajaxcleaning.com this configuration would be:
'auth_sso_domain' => '.ajaxcleaning.com', |
When you are accessing the NMIS server after this is configured you must then use the FQDN, in our development labs we use dev.opmantek.com which contains two periods, so we can configure it like so:
'auth_sso_domain' => 'dev.opmantek.com', |
Then when we browse to the servers, we use the full name of the server, e.g. nmisdev64.dev.opmantek.com and the login banner tells us that Single Sign On is configured with "dev.opmantek.com", I can enter the password and access the server.
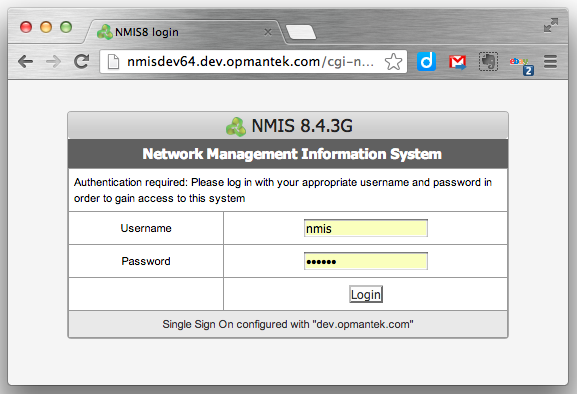
If I were to use the IP address to access the server, authentication will succeed but the cookie will not be created correctly and you will be logged out again.
When NMIS Single Sign On is configured you MUST use the Full Qualified Domain Name to access the server.
Apache (and its htpasswd tool) support a number of different password hashing mechanisms. In the past htpasswd's default mechanism was "crypt" but on most operating systems that has been changed to "md5" (as it resists dictionary attacks much better).
However: NMIS in versions up to and including 8.5G only supports the "crypt" mechanism. This means that you have to explicitely specify the appropriate method when you run htpasswd.
To add a new user to NMIS8 (while it is using htpasswd, or Apache for Authentication - and assuming that Apache has not already been integrated with LDAP, Active Directory, Radius, or the like) you will need to create a new Web Based user. This is done using the following commands, using testuser as example:
cd /usr/local/nmis8/conf # adjust that if nmis8 is not installed in the default location # for encryption method crypt: htpasswd -d users.dat testuser # ...then just follow the prompts # for encryption method md5, BUT only for NMIS newer than 8.5G: htpasswd -m users.dat testuser |
This adds the user testuser for the purpose of Authentication. Now the application needs to be also told about the users' Authorisation.
User names in many systems are not case sensitive, so NMIS will handle usernames in lower case, when adding users to Users.nmis, ensure that the name is all in LOWER CASE.
At great expense to Opmantek, support for usernames with spaces has been added, this is in the next release to be numbered 8.3.14G or higher.
NMIS 8 uses the concepts "Privileges", "Access Policy" and "Groups" to determine what resources or actions a particular user should have access to.
This infrastructure is configured using three configuration files:
Login to the NMIS Portal, as an administration user, the normal URL is http://nmisserver/cgi-nmis8/nmiscgi.pl
Using the menu access "System -> System Configuration -> Users", select "add" from the top right, and then complete the form, specifying the User which matches the user added using htpasswd, specify Privilege and Groups, using "all" if all groups are permitted, multiple groups can be selected.