...
Credentials are stored in the "credentials" database table. The actual credential information is encrypted in storage. When a Discovery is run, a device has it's credentials retrieved and tested for connection first. If these fail the list of credentials is also tested against the device. Working credentials are stored at an individual device level in the "credential" table (note - no 's' in the table name). SSH keys are tested before SSH username / password. When testing SSH, credentials will also be marked as working with sudo or being root.
NOTE - If you request a downloaded CSV, XML or JSON format (either a single credential, or the complete collection) the actual credential details will be sent. Not the encrypted string, the actual username, password, community string, etc. Any sensitive details are not displayed in the web GUI, but are made available via other formats.
...
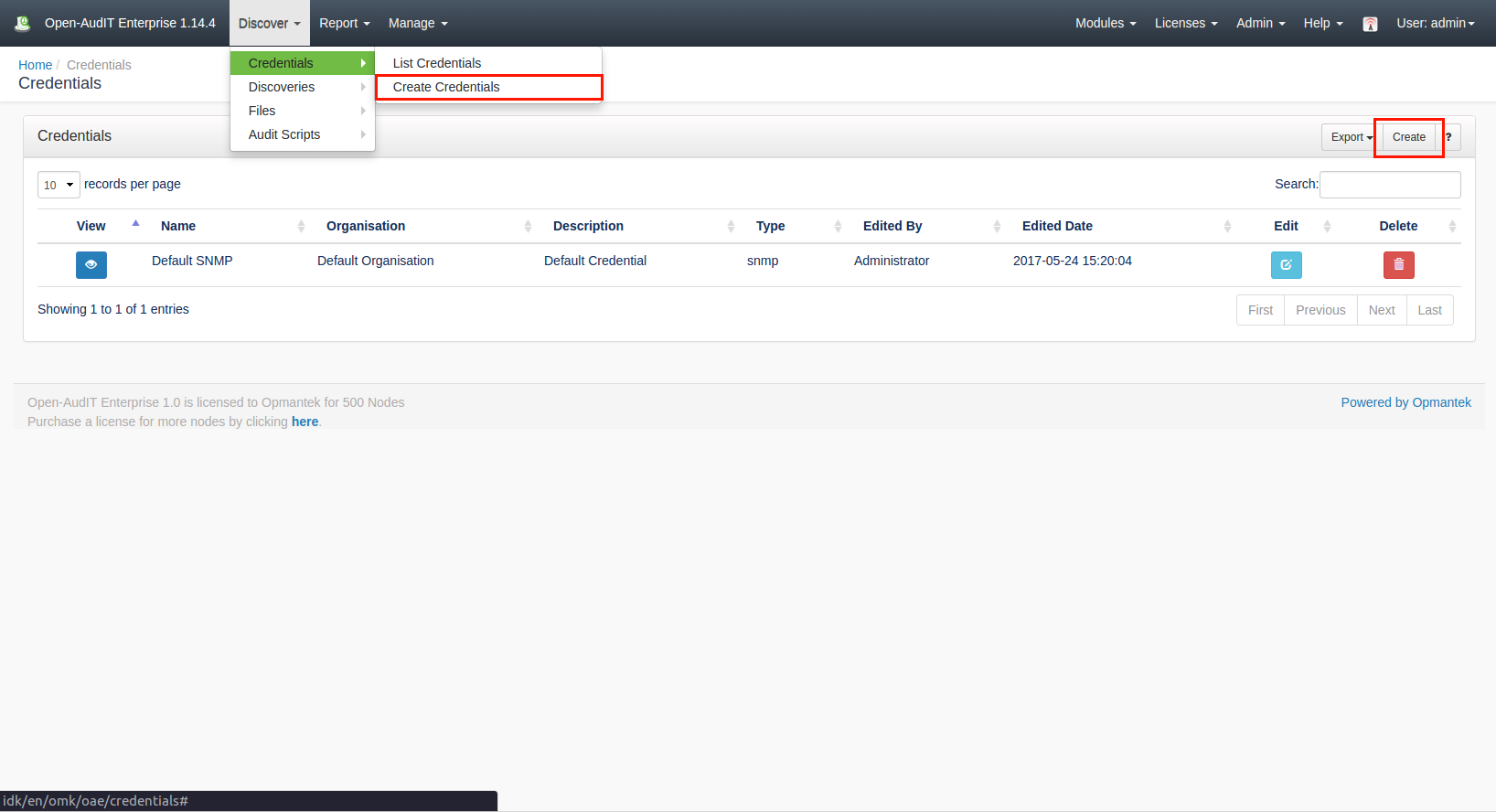
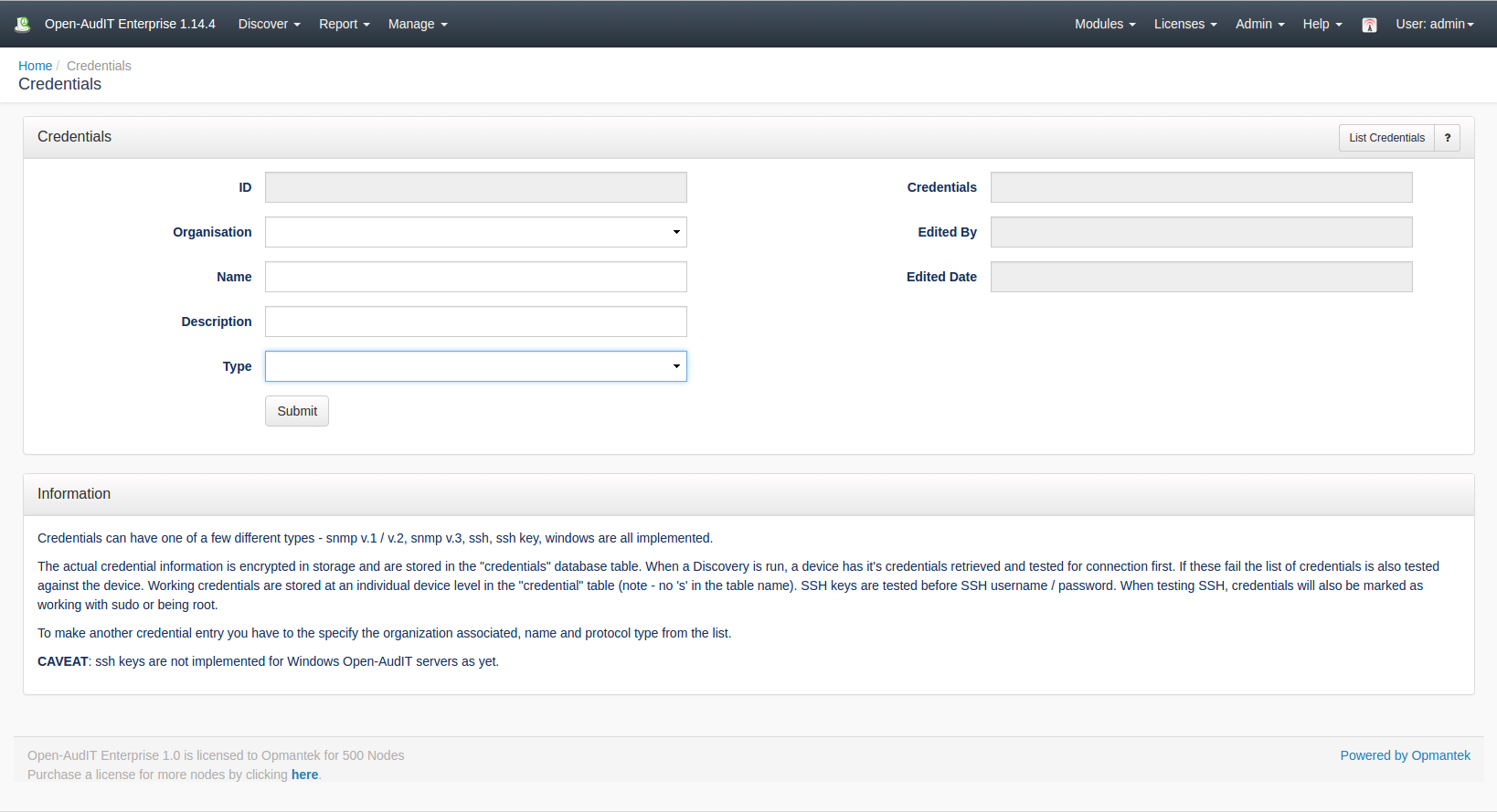
To make another credential entry use the menu and go to menu: Discover -> Credentials -> Create Credentials. Provide a name, organisation and optionally a description. Choose a type of credential. Once you do this, the additional fields will populate with the available configurable options.
SSH Keys
You should copy and paste the entire file into the textbox. In the case below, copy ALL the text.
| Code Block |
|---|
-----BEGIN RSA PRIVATE KEY----- Proc-Type: 4,ENCRYPTED DEK-Info: DES-EDE3-CBC,328refbeif03 duvbwuidnpowmpowenciubviencpomcpoenrfurehoiernfporjfoierhiuebvvn dvkjeekjvlfkvlfbvienvpoemvpoenviuberiovneporvmpoernvoiernvoiernv 9wI0nVfcdhhd8DExfgwFfWr2AoGaNYgE0TVUfRU21HQG8C+HoLysC1a4CaHsRgVy DTzGJQhfKafu2G31wt12kTycTpujeO0EyRsa4kT0KPp+IDJRtkRmEJY3UG1Xg72P jLZ/o2Ygz15ZT9GkNb9jyPCZMF3NJqL+Mz03ikKHDZvfOxA5P1XTPiXSVLzB1MJt lgP2A3vlW/eaVeVhPa6Wo9gbDm/+PzDL+rT9ZK5K8sc1AcdIJ0m9OGCQtqpwSxEB iJ07usXWXI4Cf4ex3+Oxeoineoifnoienfoiernfoiernfoermf[pef[pffed0DD FsRSBmCbsCHrzGIqk8Maqh5gjPhkerneLlH40Jeloks2tkD72UT/bYWgpvTxzVUA +LSVhR/Li+cGIebgKqKgE2sXmuIGn9UuqOvFbDudowRyrO9OtM1QsfresILmTKTA VCNKEQExL1mhsUnr1paOOMs5vZ2oO3x0S7x+QXrWGye+QK9aquZ+IQ3Z4Lb130Q4 dfvneivnoiernvoirenvoinervionreoivnreoivnoiernvoiernv/pae,fefeff W76aH+wxCuuSNWACvhfDcYXjp4dP3AD2EiuIYlvkIl0cwNrX9tmZyG37qaYDPCdW ikmDolK6tepoqS05js+RouUHvZEZg3jBxkTkI0FB+JJcOvzl9ixf3Ce/CeWkcCrb 6oGjyNEOqoFDoceIUFZGOw4tsNySyqON9a0TuToPCX5rQd57fPabnl6Tl6XUCqwz 1DZ2HyVm+k4DAzLx2BoA5urWzdlniuberovbeirvbifevnienvirenviernviner ovneiuvnieufvbiuerbviunviunervioneroivnoiernvoiernvoinervoineroi b2cmcEETwXZEzVudljkOMt7d8F2fWVcFPYSh/wneI1A7kPiWw9B1T3SRTiLS8fv4 t8pr/GvAsevzRe7q9oMAfnAYnBuWCzN++JitjgwRhj1n/WmqxqfPuRwcZ/Y8cHZb fSuJdcdlGBx7KH/7N/rRCioAc7lcRi/x+AgVs+7Cng0a5OHT4DfA6A== -----END RSA PRIVATE KEY----- |
Viewing Credential Details
...
The schema for the database is below. It can also be found in the application if the user has database::read permission by going to menu: Manage -> Database -> List, then clicking on the "credentials" table.
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
CREATE TABLE `credentials` (
`id` int(10) unsigned NOT NULL AUTO_INCREMENT,
`name` varchar(200) NOT NULL DEFAULT '',
`description` text NOT NULL,
`type` enum('aws','basic_auth','cim','ipmi','mysql','netapp','other','snmp','snmp_v3','sql_server','ssh','ssh_key','vmware','web','windows') NOT NULL DEFAULT 'other',
`credentials` text NOT NULL,
`org_id` int(10) unsigned NOT NULL DEFAULT '1',
`edited_by` varchar(200) NOT NULL DEFAULT '',
`edited_date` datetime NOT NULL DEFAULT '2000-01-01 00:00:00',
PRIMARY KEY (`id`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8; |
...
NOTE - org_id is not used at present.
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
id: 26
name: Mark at home
description:
type: ssh
credentials: 12389RdkKYFQrwZF3bfBeHSyHhAXdIbh2i22MsSdsnpCO72lQGoRnlpKfW+AETgmCOhIAe3NQmRucMncsaGTyeczshUCuv1iqTuk8ZT3sHyGkDPkq/FiX1z6guUL123/
org_id: 0
edited_by: Administrator
edited_date: 2017-06-08 10:11:12 |
...
When requesting a credentials details via the API, the credentials section will be decrypted.
API Routes
Request Method | ID | Action | Resulting Function | Permission Required | URL Example | Notes | Example Response |
|---|---|---|---|---|---|---|---|
| POST | n |
| create | credentials::create | /credentials | Insert a new credentials entry. | credentials_create.json | ||
| GET | y |
| read | credentials::read | /credentials/{id} | Returns a credentials details. | credentials_read.json | |
| PATCH | y |
| update | credentials::update | /credentials/{id} | Update an attribute of a credentials entry. | credentials_patch.json | ||
| DELETE | y |
| delete | credentials::delete | /credentials/{id} | Delete a credentials entry. | credentials_delete.json | |
| GET | n |
| collection | credentials::read | /credentials | Returns a list of credentials. | credentials_collection.json |
Web Application Routes
Request Method | ID | Action | Resulting Function | Permission Required | URL Example | Notes |
|---|---|---|---|---|---|---|
| GET | n | create | create_form | credentials::create | /credentials/create | Displays a standard web form for submission to POST /credentials. |
| GET | y | update | update_form | credentials::update | /credentials/{id}/update | Show the script details with the option to update attributes using PATCH to /credentials/{id} |
| GET | n | import | import_form | credentials::create | /credentials/import | Displays a standard web form for submission to POST /credentials/import. |
| POST | n | import | import | credentials::create | /credentials/import | Import multiple credentials using a CSV. |