Introduction
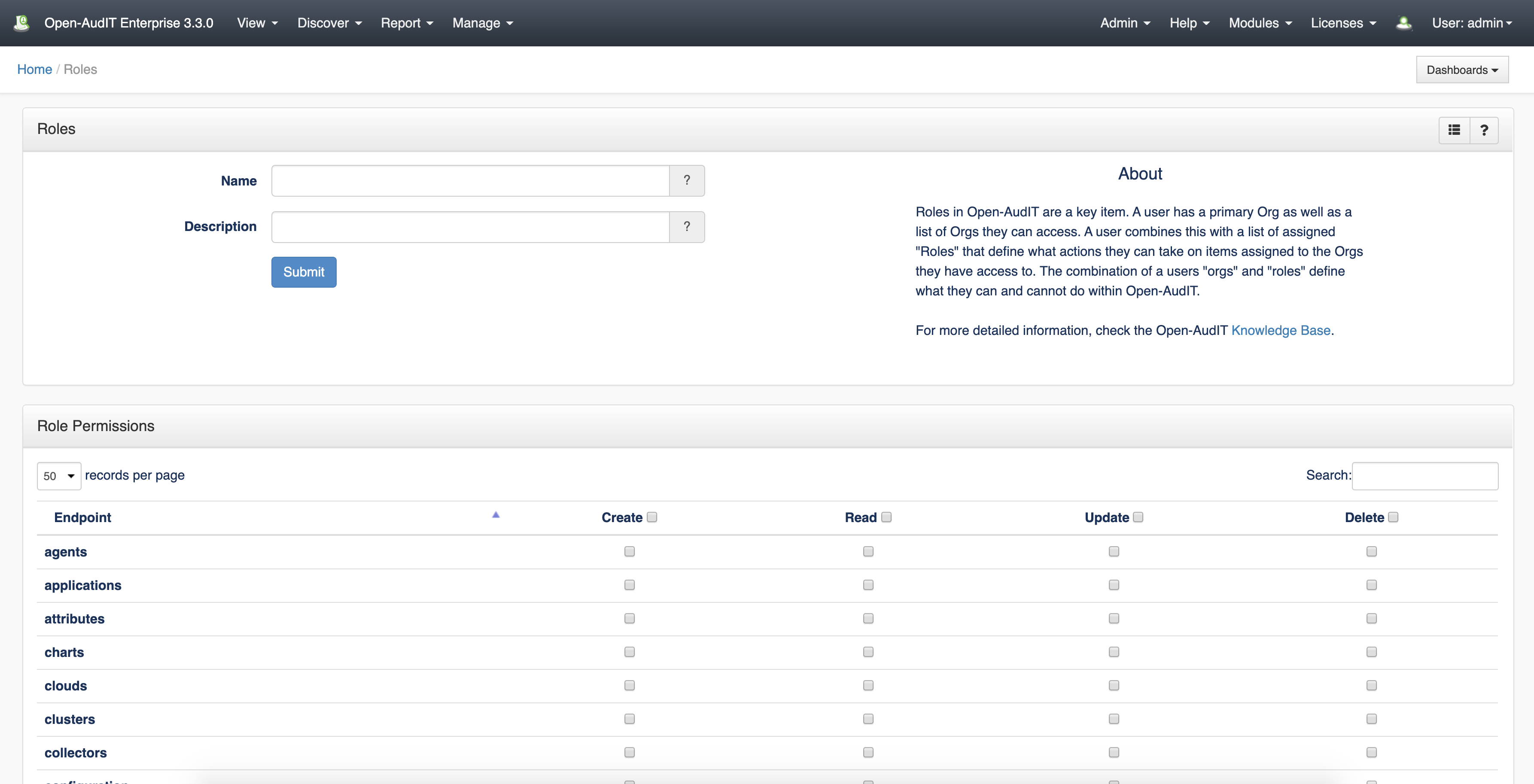
The "Roles" endpoint allows you to manage the set of permissions(Create, Read, Update, Delete) that are granted to the users and are applied to each endpoint.
How Does it Work?
The primary method for authorization (what a user can do) is now based on the users' Roles. Roles are defined as admin, org_admin, reporter, and user by default. Each role has a set of permissions (Create, Read, Update, Delete) for each endpoint. Standard roles as shipped should cover 99.9% of use-cases. The ability to define additional roles and edit existing roles is enabled in Open-AudIT Enterprise.
Creating a Role Entry
Join Paul McClendon, an Opmantek Support Engineer, as he demonstrates how to create different roles in Open-AudIT.
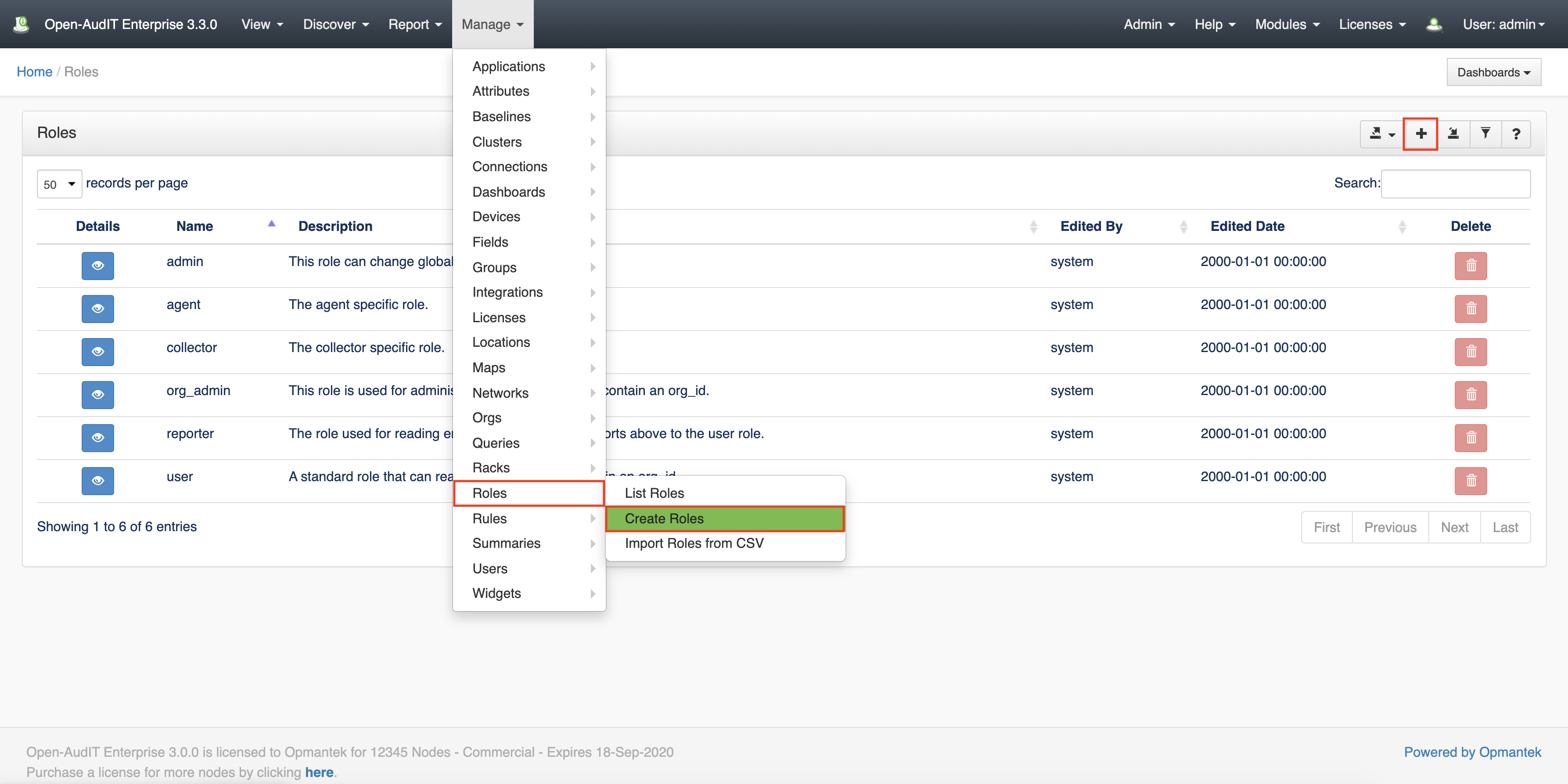
A roles entry can be created using the web interface if the current user logged in has a defined role that contains the user::create permission. Go to menu: Manage -> Roles -> Create Roles. Also can be created from the Roles View, using the "+" button.
To add a new user to Open-AudIT you have to provide the details of that person, assign the organization, select the relevant Roles (multiple roles can be selected), select if the user is active or not, etc. In addition, you must grant permission to that user to access one or more organizations. It is important to notice that selecting a parent organization will automatically provide access to its children.
View Role Details
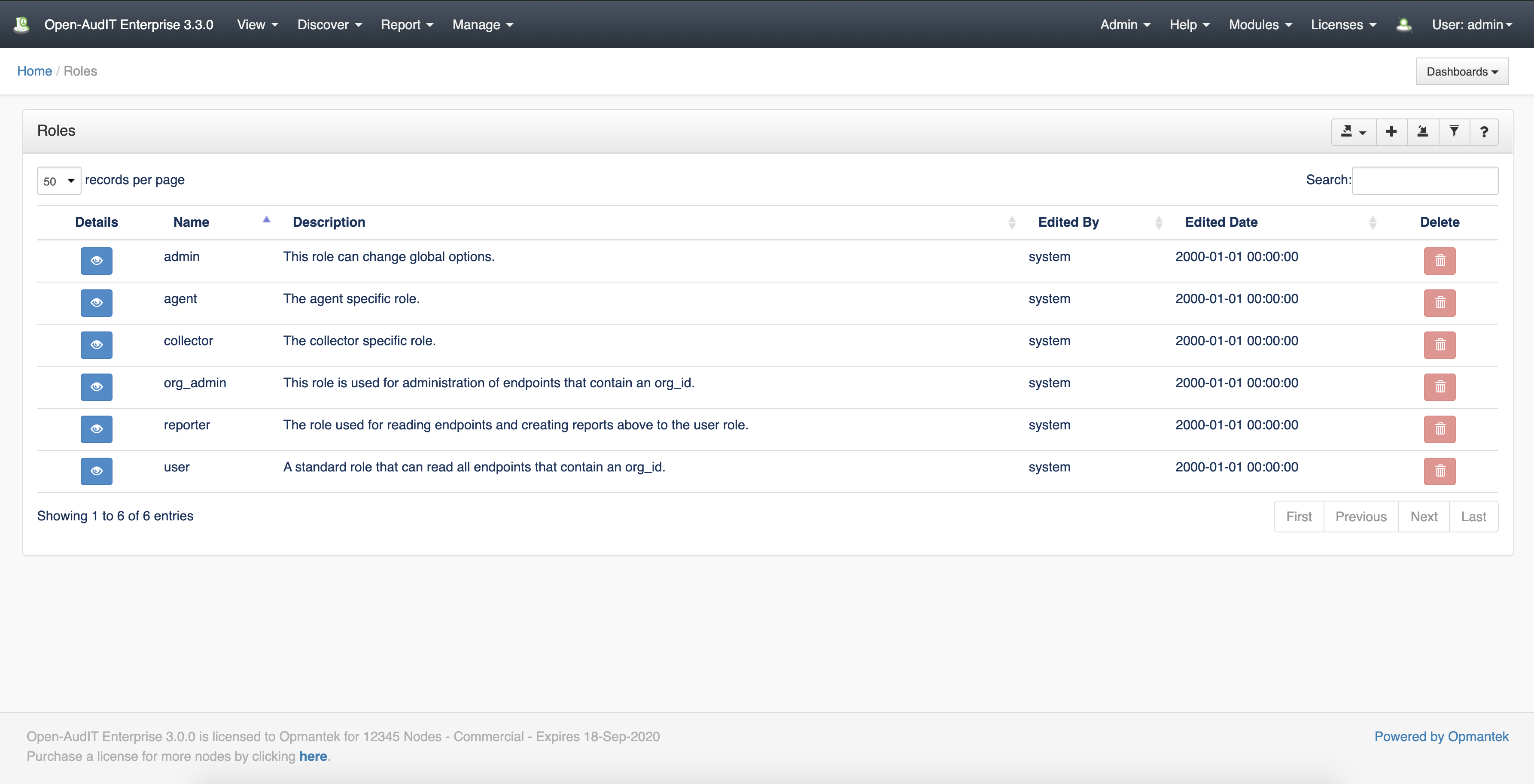
Go to menu: Manage-> Roles -> List Roles.
Database Schema
The database schema can be found in the application is the user has database::read permission by going to menu: Admin -> Database -> List Tables, then clicking on the details button for the table.
API / Web Access
You can access the collection using the normal Open-AudIT JSON based API. Just like any other collection. Please see The Open-AudIT API documentation for further details.
Default Items
Shipped are a set of default items. These can be found by going to menu: Help → Defaults → Roles.